Featured
Featured
Shadow of Deception - Attribution
In the shadowy world of international espionage, where nations dance a delicate dance of secrecy and power, the concept of attribution takes center stage. As cyber threats loom large, experts and governments alike strive to unravel the mysteries behind the attacks that threaten to disrupt the global order.
In this episode, Andrew Amaro from our team delves deep into the complexities of attribution, exploring how nation-states meticulously conceal their involvement to maintain deniability and strategic advantage. From sophisticated cyberattacks to covert operations, every move carries weight, shaping the delicate balance of power on the global stage.
But as the stakes escalate, so too does the risk of misattribution. With potentially dire consequences looming, our experts uncover the challenges of accurately identifying perpetrators in a world where deception reigns supreme. From intentional misinformation to the manipulation of digital fingerprints, the line between truth and deception becomes increasingly blurred.
Join us as we navigate the murky waters of international espionage, shedding light on the elusive nature of attribution and the high-stakes game of cat and mouse that defines the modern age of cyber warfare.
Klavansecurity.com #soc2 #managedsecurity
7
views
1
comment
Anything to declare? - Security Travel Tips
🌍✈️ Heading on a getaway? Before you jet off, tune in to our latest episode of "Anything to Declare?" where we unpack essential Security Travel Tips to ensure your journey is smooth, safe, and stress-free! From protecting your devices on the go to navigating public Wi-Fi with confidence, we've got you covered. Don't miss out on expert insights and insider tricks to safeguard your privacy and personal information while exploring the world. Whether you're a seasoned globetrotter or a first-time adventurer, these travel tips are a must-have in your arsenal. Hit play now and embark on your next adventure with peace of mind! #TravelSmart #SecurityTips #ExploreSafely 🛡️🔒🌟
55
views
1
comment
May I Use Your Bathroom - Perception vs Reality - Security in the Eye of the Beholder
Join us as we unravel the illusions of invulnerability surrounding security in today's world. From underestimating threats to overlooking asset value, we confront common misconceptions and vulnerabilities.
In this podcast, we explore the dangers of complacency and the importance of awareness in maintaining effective security protocols. We delve into cyber threats, alert fatigue, and the exploitation of data breaches by cybercriminals.
Discover the significance of external assessments in identifying security gaps and fortifying defenses. We emphasize the relentless nature of criminals and the need for proactive measures to protect facilities and assets.
In a world where security breaches are rampant, our podcast serves as a reminder that true security lies in proactive diligence and preparedness. Tune in and stay informed. Thank you for joining us.
28
views
1
comment
Infostealers, Ameaca e ecossystema - ciber seguranca em Portugal
Andrew Amaro - CSO KlavanSecurity.com #Portugal #Ciberseguranca
Bem-vindo ao nosso primeiro episódio totalmente em português! Estamos animados para trazer a vocês uma série de discussões sobre segurança cibernética, ameaças digitais e os segredos sombrios da internet. Neste episódio inaugural, vamos mergulhar fundo no mundo dos infostealers, explorar as últimas ameaças e desvendar os ecossistemas da dark web. E o melhor de tudo, este é apenas o começo! Prepare-se para uma jornada fascinante através dos corredores virtuais da cibersegurança. Fiquem ligados, pois mais episódios emocionantes estão a caminho. Estamos ansiosos para compartilhar mais insights e informações valiosas com vocês.
20
views
1
comment
Cyber Risk Quantification - Your Cyber Spidey Sense
Alright, picture yourself as the superhero guardian of a bustling metropolis, defending it from cyber villains lurking in the digital shadows. Your mission? To safeguard the city's precious data and infrastructure from the clutches of nefarious hackers!
Now, imagine cyber risk quantification as your superpower—a bit like Spider-Man's spidey sense or Batman's detective skills. It's your ability to analyze the city's digital landscape, identifying potential threats and vulnerabilities before they strike.
As the superhero, you use your cyber risk quantification powers to assess the strength of the city's defenses against cyber villains. You gauge the likelihood and impact of various cyber attacks, from sneaky phishing schemes to full-blown cyber invasions.
But fear not! With your superpower, you can develop strategic plans to fortify the city's cyber defenses. Maybe you'll deploy Iron Man's high-tech encryption to safeguard sensitive data or unleash Wonder Woman's lasso of truth to uncover hidden vulnerabilities.
And just like in a comic book, every victory against cyber villains earns you experience points and unlocks new abilities to strengthen the city's resilience against future threats.
So, don your cyber cape, summon your inner superhero, and get ready to vanquish cyber villains with the power of cyber risk quantification! The city is counting on you to save the day!
26
views
2
comments
Shadow of Deception - Attribution
In the shadowy world of international espionage, where nations dance a delicate dance of secrecy and power, the concept of attribution takes center stage. As cyber threats loom large, experts and governments alike strive to unravel the mysteries behind the attacks that threaten to disrupt the global order.
In this episode, Andrew Amaro from our team delves deep into the complexities of attribution, exploring how nation-states meticulously conceal their involvement to maintain deniability and strategic advantage. From sophisticated cyberattacks to covert operations, every move carries weight, shaping the delicate balance of power on the global stage.
But as the stakes escalate, so too does the risk of misattribution. With potentially dire consequences looming, our experts uncover the challenges of accurately identifying perpetrators in a world where deception reigns supreme. From intentional misinformation to the manipulation of digital fingerprints, the line between truth and deception becomes increasingly blurred.
Join us as we navigate the murky waters of international espionage, shedding light on the elusive nature of attribution and the high-stakes game of cat and mouse that defines the modern age of cyber warfare.
Klavansecurity.com #soc2 #managedsecurity
7
views
1
comment
Will you know what to do, if your organization gets cyber attacked? - Incident Response Plan
Unlock the Secrets of Incident Response with Andrew Amaro from Klavan Security and John Hipp from Arctic Wolf!
Dive into the world of cybersecurity as we unravel expert insights, actionable tips, and real-world scenarios. Join us on our podcast journey to bolster your incident response strategy and defend against digital threats!
Tune in now for a cyber security masterclass you won't want to miss!
14
views
SE 01, EP 10 - Cyber Insurance - Full Solution or Another Layer in your Cyber Strategy?
In this episode of the Klavan podcast, host Andrew Amaro sits down with an industry expert to delve into the world of cyber liability insurance. They discuss the evolving landscape of the industry, highlighting key changes and trends. Listeners gain valuable insights into preparing for applying for coverage and discover practical strategies to save on premiums. Tune in to learn how to navigate the complexities of cyber liability insurance and protect your assets in today's digital age.
31
views
EP 9 - Cold War vs Modern Cyber Spy techniques - NEW Bit!
Powered by KlavanSecurity.com - Host Andrew Amaro
Explore the evolution of espionage from the Cold War era to modern digital cyber techniques:
Join us as we delve into the captivating world of espionage, tracing its roots from ancient civilizations to the present day. In the aftermath of World War II, the Cold War emerged as a period of intense rivalry between the United States and the Soviet Union, characterized by political, economic, and military competition. Learn about the covert operations, proxy wars, and nuclear brinkmanship that defined this era, ultimately culminating in the dissolution of the Soviet Union in 1991.
But espionage didn't end with the Cold War—it evolved.
Discover how spy techniques have transitioned from traditional Cold War methods to modern digital cyber techniques. From human intelligence (HUMINT) and covert communications to cyber espionage and electronic surveillance, uncover the tools and tactics used by spies to gather intelligence and maintain secrecy. Explore the parallels and differences between Cold War spy operations and contemporary cyber espionage, as we analyze the nature of operations, scale and reach, speed and automation, and attribution and deniability.
Join us as we unravel the mysteries of espionage past and present, exploring the enduring allure of spies and their clandestine activities in the shadowy world of intelligence gathering.
61
views
EP 8 - The Silent Threat: Critical Infrastructure - Water
In this episode of Shadow Tactics, we delve into the unseen but potentially devastating consequences of cyberwarfare on critical infrastructure, focusing specifically on water treatment facilities. As the world becomes increasingly interconnected and reliant on digital systems, the vulnerability of essential services to cyber attacks becomes more apparent.
Join us as we explore the chilling scenario of a cyber attack on a water treatment facility. What happens when hackers breach the defenses of these vital facilities? How does cyberwarfare intersect with power projection strategies of nation-states? Our experts dissect the tactics, motives, and potential consequences of such attacks, highlighting the urgency of cybersecurity measures in safeguarding our public health and safety.
From the manipulation of water quality to the disruption of supply chains, the implications of a cyber attack on water treatment facilities extend far beyond the digital realm. As governments and malicious actors vie for control and influence, understanding the intricacies of cyberwarfare becomes paramount in defending against this silent threat.
Tune in to Shadow Tactics as we navigate the murky waters of cyberwarfare and its implications for critical infrastructure, shedding light on the unseen battles waged in the digital domain.
28
views
EP7 - Cywareness visits Klavan HQ
Welcome to the latest episode of our podcast - Shadow Tactics: Insights into security, where Andrew Amaro Klavan's Chief Security Officer (CSO) delves into the world of cybersecurity with Ari Lev, Sales Manager at Cywareness. In this insightful conversation, they explore the critical importance of security awareness, dissect the features of the Cywareness platform, delve into the necessity for multilingual support, dissect operational security (OPsec), social engineering, phishing attacks, discuss the thriving security community, and unravel the power of strategic partnerships. Join us as we uncover the complexities of cybersecurity and the strategies needed to stay ahead in an ever-evolving digital landscape.
51
views
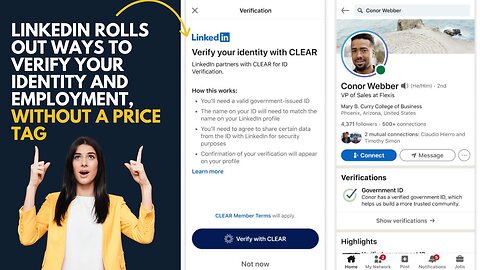
LinkedIn Verification, Data Privacy and Benefits
Klavan's new episode, on LinkedIn Verification, Persona and CLEAR companies. What are we gaining or losing by verifying our Identity for our social media accounts.
#dataprivacy #verification #online
7
views
LEO Sat Security - Free Internet, Free of Security? Free Satellites for all? Space Pirates?
When satellite tech becomes cheaper, becomes easier to make, becomes available to all, just like TVs and mobile phones, what then? What should we expect or do to prepare?
5
views
Axel Foley is a Social Engineer
This one here is a throwback to an old channel we had, but still very relevant today.
Detective Alexander James "Axel" Foley is a fictional character, portrayed by Eddie Murphy, and is the titular protagonist of the Beverly Hills Cop film series.
In this scene, Axel, demonstrates how to socially engineer your way in and out of a situation, in 5 easy steps.
4
views
Cyber Security - Before, During and After the Super Bowl
Andrew Amaro, Founder and Chief Security Officer at Klavan Group speaks from Allegiant Stadium in #LasVegas, discussing the upcoming Super Bowl 58 between the San Francisco 49ers and the Kansas City Chiefs.
He raises concerns about cyber security risks associated with #streaming, #gambling, and #ticketpurchasing during major events like the #superbowl .
Andrew warns against accessing #unauthorized streams or falling for #scams , emphasizing the importance of staying safe online.
Hope you enjoy!
KlavanSecurity.com
#taylorswift #kansascitychiefs #cyberdefense #security #defensivesecurity #online #onlinefraud #safetyawareness
8
views
Cyber Incident - To negotiate or Not To negotiate
What to do? What to do?
Car problems = Call a mechanic
Health problems = Call a Doctor
Legal problems = Call a Lawyer
Cyber problems = Call KlavanSecurity.com ☎
But wait, hold your virtual horses! In this quirky new segment, we're diving deep into the realm of cyber chaos. We'll show you what to do and what definitely not to do. And hey, if you accidentally wander into the "what not to do" territory, fear not! We've got your digital back with some clever solutions. So buckle up and get ready for a cyber adventure like no other! Enjoy the ride! 🚗💻
#ai,#llm,#scams,#btc,#crypto,#security,#negotiations,#cyber,#cybersecurity
9
views
CEO and his Physical and Cyber Incident
In this clip, Andrew, Founder and Chief Security Officer at Klavan Group, discusses the story of David Reynolds, a successful CEO in New York, who becomes the target of a malicious hacker named Ethan. Using his hacking skills, Ethan scours social media for David's details and launches a phishing campaign. He gains access to sensitive information, infiltrates the car rental company David uses, and tracks his movements during a business trip. Ethan orchestrates break-ins at David's hotels and infiltrates his company's security system, planting listening devices and malware. Strange occurrences hint at the looming threat, but David remains unaware of the digital web around him. Eventually, Ethan's grand plan is unveiled, shaking the tech industry forever.
So, what can we learn from this story? It highlights the importance of a holistic approach to security, integrating physical and cyber measures to protect against evolving threats. With a comprehensive risk assessment, organizations can identify vulnerabilities and prioritize security measures. By implementing a combination of physical and cyber security measures, continuously monitoring for threats, and fostering collaboration across departments, organizations can better protect their assets and maintain resilience in the face of security threats.
#airport,#hotels,#vacation,#ceolife,#protection,#cybersecurity,#crypto,#ai,#chatgpt
6
views
Aftermath of Ransomware - What else to do?
Andrew from Klavan Group discusses the critical issue of ransomware and its significant impact on organizations. He emphasizes the damage caused to trust between clients and organizations, the financial losses incurred, and the risk to individuals associated with these organizations. Andrew highlights the growing trend of ransomware groups curating data obtained in attacks to create profiles for sale on the dark web.
The focus then shifts to the aftermath of a ransomware attack, where Andrew stresses the importance of reporting data breaches, conducting impact assessments, and notifying affected parties. He discusses the potential fraud and social engineering scenarios that may follow, emphasizing the need for organizations to take responsibility for the security of sensitive information.
Andrew provides practical steps for mitigating risks, such as providing credit monitoring for employees and individuals, notifying third-party associates, and engaging in a comprehensive assessment of the data and individuals involved. He concludes by urging vigilance and mutual support among organizations to collectively combat the ongoing threat of ransomware.
KlavanSecurity.com
Ransomware Statistics: dbd.knack.com/prism
#ai,#llm,#crypto,#security,#cybersecurity,#ransomware,#klavan,#managedsecurity,#incidentresponse,#cyberattack
28
views