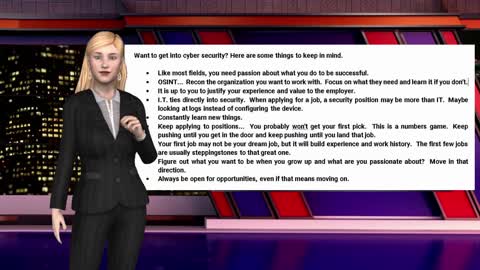
Do you want to get into Cybersecurity?
Do you want to get a job in the cybersecurity industry? Here are a few things to think about if you re just starting.
21
views
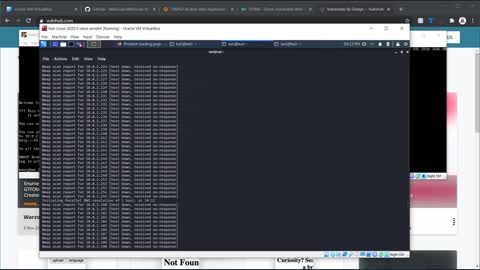
Anti-forensics with the USB Rubber Ducky (Rubber Ducky Frame Job)
In this episode, we will be covering the USB Rubber Ducky from Hak5 and how it could be used for anti-forensics.
If you would like to support our channel and content, we have printed/ebook publications with in depth on Amazon [https://amzn.to/3nL9RsC] and merch on Teespring [https://teespring.com/stores/cybersec...]
67
views
The OSINT Cyber WAR in Review: January 18th, 2021
The OSINT Cyber WAR in Review: January 18th, 2021
Top 5 Stories
* Signal Operational Again After Daylong Outage
* WhatsApp Responds To Concerns Over Privacy Policy Update
* Hackers Used 4 Zero-Days To Infect Windows And Android Devices
* Vaccine Research Companies are the Target of New Ransomware Attacks
* Space Force joins the intelligence community
---
Top 5 Exploits
* Microsoft Spooler Local Privilege Elevation
* Cisco UCS Manager 2.2(1d) Remote Command Execution
* Life Insurance Management System 1.0 multiple exploits
* Online Hotel Reservation System 1.0 multiple exploits
* E-Learning System 1.0 - Authentication Bypass & RCE
---
Top 5 Darknet News
* Joker's Stash Carding Market to Call it Quits
* Cryptocurrency Exchange Owner Sentenced to Prison
* HugBunter is Requesting Proof-of-Life from Onion Service Admins
* Yellow Brick Market is Gone Once Again
* DarkMarket Has Been Seized
10
views
The OSINT Cyber WAR in Review January 11, 2021
This is a quick video review of what is in the Cyber WAR for January 11th, 2021. Enjoy and subscribe to the report: https://informationwarfarecenter.com/CIR
Top 5 Stories
1. Rioters Had Access To Capitol Computers.
2. Sealed U.S. Court Records Exposed
3. FBI, CISA, NSA Officially Blame Russia for SolarWinds Cyber Attack
4. Ransomware Data Published via DDoSecrets.
5. British Court Rejects U.S. Request to Extradite WikiLeaks' Julian Assange
Top 5 Exploits
1. NTLM BITS SYSTEM Token Impersonation
2. Backdoor.Win32.Xtreme.yvp Privilege Escalation
3. Backdoor.Win32.Agent.dcbh Privilege Escalation
4. WordPress wpDiscuz 7.0.4 Shell Upload
5. WordPress Autoptimize Shell Upload
Top 5 Darknet News
1. Finnish Customs to Sell Almost 2,000 Seized Bitcoin
2. Four Sentenced to Prison for Darkweb Drug Distribution
3. Virginia Man Sold Pressed Adderall on Empire Market
4. CEO of Bitcoin ATM Company Indicted for Money Laundering
5. Employee Credentials On Darknet: over 500,000 leaked
191
views
A Pentest that is Fast, Good, Cheap, and we own you afterwards
A Pentest that is Fast, Good, Cheap, and we own you afterwards. Yes, some companies have extremely unreasonable expectations. Be very careful and manage their expectations or learn to walk away.
6
views
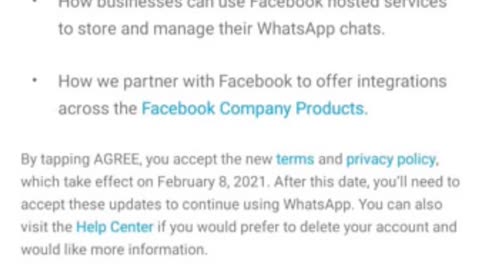
WhatsApp removes privacy and Signal Messenger is an option to keep it
Facebook has a long history of privacy lapses. I mean some real serious ones. While WhatsApp was still able to keep a fair distance from Facebook’s unreliable privacy practices, that benefit is soon going away, as the messaging app has decided to enforce new usage terms that give its parent company more control over your WhatsApp data including financial data with its WhatsApp Pay.
If you want a better and more reliable messaging service, the Signal Messenger app is a great option. Here are the benefits that WhatsApp no longer has.
• Open Source
• Self-destruct messages
• All your data, including metadata is not stored by signal servers
• Text, Voice, and video quality is encrypted end-to-end.
• Both cryptography experts and privacy advocates recommend Signal.
14
views
The Cyber Secrets "Secrets"... Publications and Social Media groups
This video talks about the Cyber Secrets publications and Social Media resources.
24
views
iPhone/iPad Forensics - Logical Copy with CSI Linux
This episode covers iPhone/iPad Forensic Logical images using CSI Linux with idevicebackup2.
If you would like to support our channel and content, we have printed/ebook publications with in depth on Amazon [https://amzn.to/3nL9RsC] and merch on Teespring [https://teespring.com/stores/cybersec...]
78
views
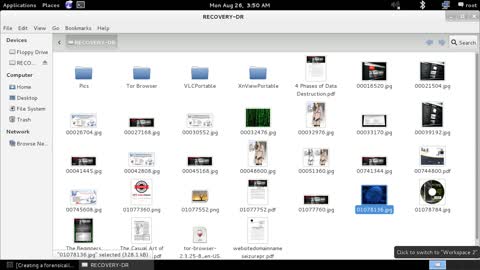
Computer Forensics Imaging - Imaging a drive in a forensic manner
This episode covers what forensic imaging means in computer forensics and why it is so important.
If you would like to support our channel and content, we have printed/ebook publications with in depth on Amazon [https://amzn.to/3nL9RsC] and merch on Teespring [https://teespring.com/stores/cybersec...]
53
views
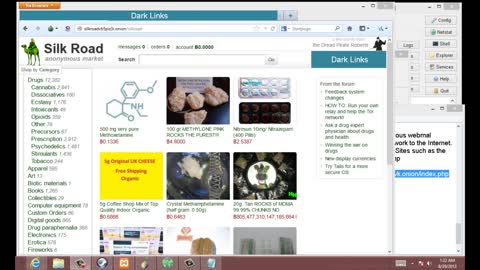
Tor Darknet and hidden services
In this episode we will be covering Tor hidden services on windows using vidalia within the Darknet/Dark web.
If you would like to support our channel and content, we have printed/ebook publications on Amazon [https://amzn.to/3nL9RsC] and merch on Teespring [https://teespring.com/stores/cybersec...]
102
views
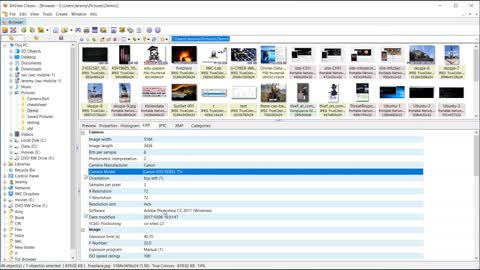
Analyzing a graphic image EXIF with XnView
In this episode, we will cover how to analyze a graphic image with EXIF information using XnView. The EXIF can also include GPS location data.
If you like the video, please like and share it so other people can see it.
If you would like to support our channel and content, we have printed/ebook publications on Amazon [https://amzn.to/3nL9RsC] and merch on Teespring [https://teespring.com/stores/cybersecrets]
20
views
Learn Web App Hacking by doing it the legal way!
In this episode of Cyber Secrets, we will cover resources you can start off with when trying to practice web application hacking in a lab environment. Of course you will need to learn the basics and have tools to help you, but then what? We cover some of the many resources you have available to practice your tradecraft.
92
views
Breach Leaks and Data Breaches - Cyber Secrets
This episode of Cyber Secrets covers breach leaks and hacker databases filled with (potentially) your user information and passwords.
233
views
Anonymity on the Internet
Originally aired in January 2013, this episode has been remastered and covers anonymity on the Internet
215
views
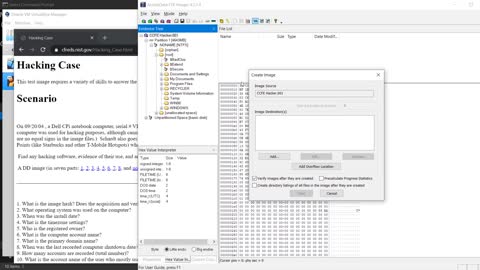
Forensic image booting in VirtualBox with FTK Imager
In this episode, we will walk through how to take a forensic copy of a hard drive, make a copy with FTK Imager, convert the image to a .vmdk file with VBoxManage, and boot it in a virtual machine with VirtualBox.
This is useful for forensic investigations, DFIR, malware analysis, and even data recovery.
If you would like to support our channel and content, we have printed/ebook publications with in depth on Amazon [https://amzn.to/3nL9RsC] and merch on Teespring [https://teespring.com/stores/cybersec...]
15
views
OSINT Framework Demo - Cyber Secrets
This episode will walk through a couple of nice features inside the OSINT Framework [https://osintframework.com/]. It is a great resource to start from when doing reconnaissance or investigating.
If you like the video, please like and share it so other people can see it.
If you would like to support our channel and content, we have printed/ebook publications on Amazon [https://amzn.to/3nL9RsC] and merch on Teespring [https://teespring.com/stores/cybersecrets]
18.5K
views
Powershell using PsExec
Cyber Secrets: Just the Tip video showing how to use PsExec over a network in Powershell.
47
views